Summary
The Casa OS Login page has disclosed the username enumeration vulnerability in the login page which was patched in CasaOS v0.4.7.
Details
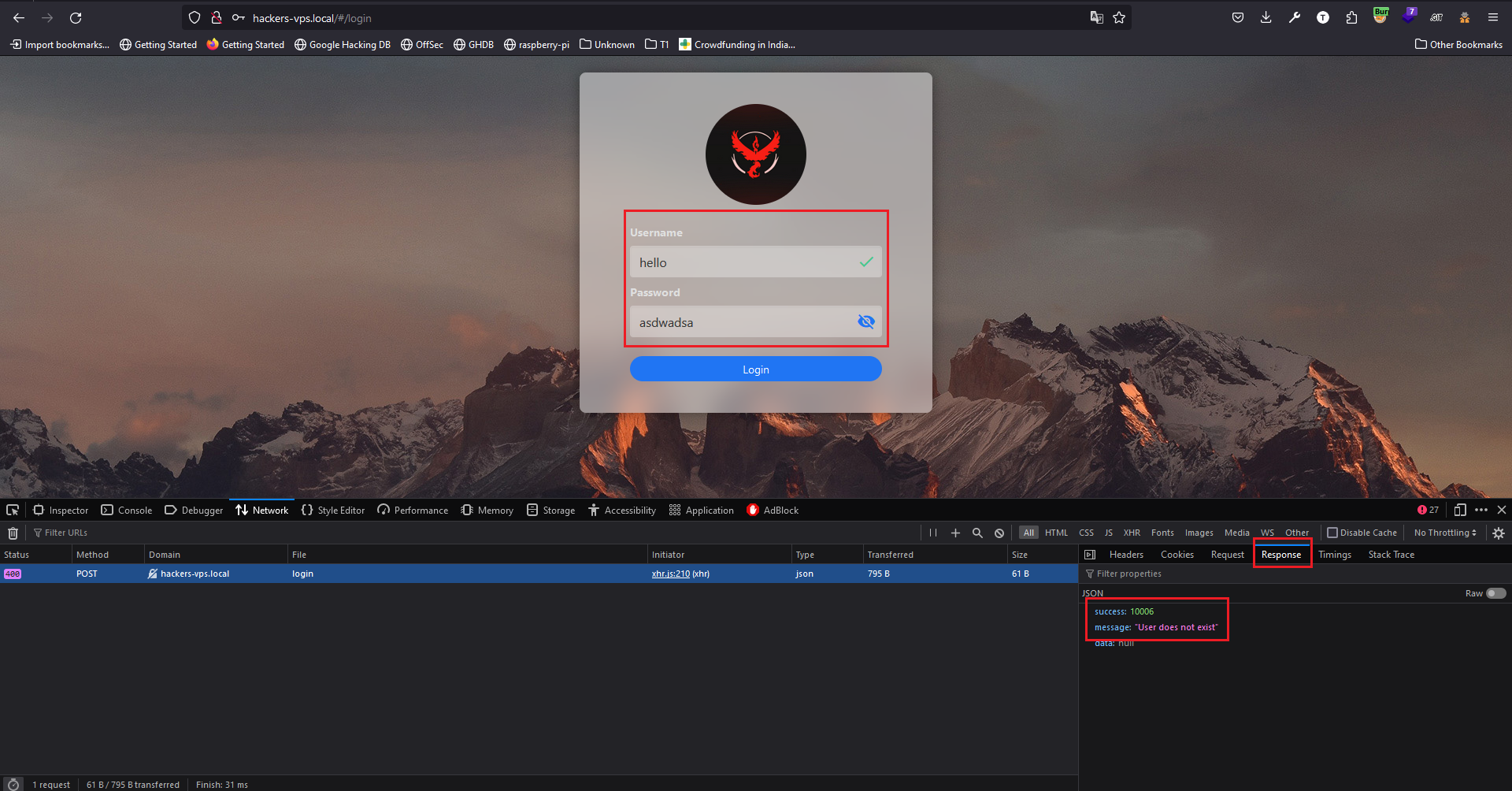
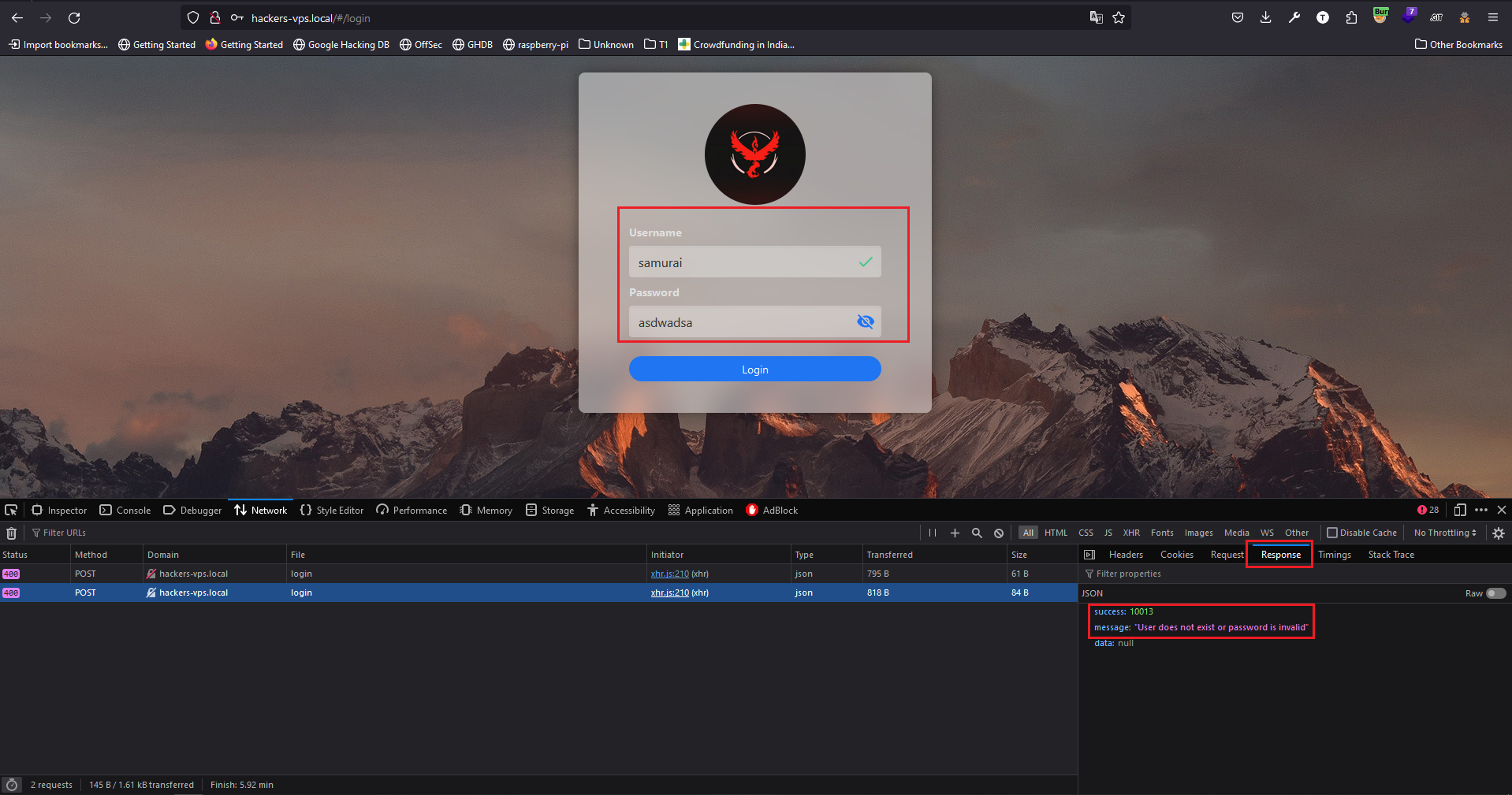
It is observed that the attacker can enumerate the CasaOS username using the application response. If the username is incorrect the application gives the error "User does not exist" with success code "10006", If the password is incorrect the application gives the error "User does not exist or password is invalid" with success code "10013".
PoC
- If the Username is invalid application gives "User does not exist" with success code "10006".
- If the Password is invalid application gives "User does not exist or password is invalid" with success code "10013".
Impact
Using this error attacker can enumerate the username of CasaOS.
The logic behind the issue
The logic behind the issue
If the username is incorrect, then throw an error "User does not exist" with success code "10006", else throw an error "User does not exist or password is invalid" with success code "10013".
This condition can be vice versa like:
If the password is incorrect, then throw an error "User does not exist or password is invalid" with success code "10013", else throw an error "User does not exist" with success code "10006".
Mitigation
Since this is the condition we have to implement a single error which can be "Username/Password is Incorrect!!!" with single success code.
References
Summary
The Casa OS Login page has disclosed the username enumeration vulnerability in the login page which was patched in
CasaOS v0.4.7.Details
It is observed that the attacker can enumerate the CasaOS username using the application response. If the username is incorrect the application gives the error "User does not exist" with success code "10006", If the password is incorrect the application gives the error "User does not exist or password is invalid" with success code "10013".
PoC
Impact
Using this error attacker can enumerate the username of CasaOS.
The logic behind the issue
The logic behind the issue
If the username is incorrect, then throw an error "User does not exist" with success code "10006", else throw an error "User does not exist or password is invalid" with success code "10013".
This condition can be vice versa like:
If the password is incorrect, then throw an error "User does not exist or password is invalid" with success code "10013", else throw an error "User does not exist" with success code "10006".
Mitigation
Since this is the condition we have to implement a single error which can be "Username/Password is Incorrect!!!" with single success code.
References