Version v2.2.4 IS OUT !!
Check the changelog here Changelog of v2.2.4
- Badges 📌 :
- Support me 💰 :
- Versions 🔐 :
- Blogs & Articles 📰 :
- Overview 📙 :
- Features 📙 :
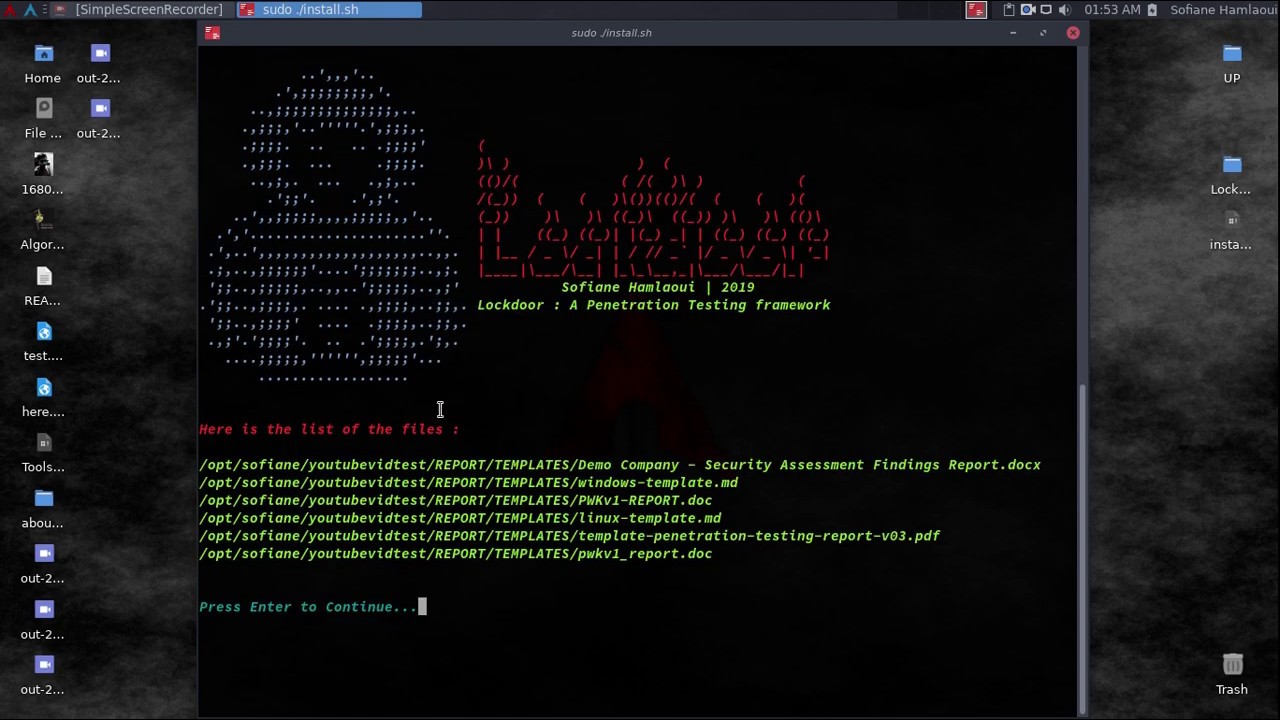
- Screenshots 💻 :
- Demos 💻 :
- Installation 🛠️ :
- Lockdoor Tools contents 🛠️ :
- Lockdoor Resources contents 📚 :
- Information Gathering 🔎 :
- Crypto 🛡️:
- Exploitation ❗:
- Networking 🖧 :
- Password Attacks ✳️:
- Post Exploitation ❗❗:
- Privilege Escalation
⚠️ : - Pentesting & Security Assessment Findings Report Templates 📝 :
- Reverse Engineering ⚡ :
- Social Engineering 🎭:
- Walk Throughs 🚶 :
- Web Hacking 🌐 :
- Other 📚 :
- Contributing ℹ️ :
- On Paypal : https://www.paypal.com/paypalme2/SofianeHamlaoui
- BTC Addresse : 1NR2oqsuevvWJwzCyhBXmqEA5eYAaSoJFk
Config file checking.
Updating the tools.
Showing the current version of Lockdoor by -v arg.
checking the version and asking for possible update.
Making it easier to customize.
No added tools for the moment.
Fixing the docker misconfiguration, the docker version now works perfectly.
- Information Gathring Tools (21)
- Web Hacking Tools(15)
- Reverse Engineering Tools (15)
- Exploitation Tools (6)
- Pentesting & Security Assessment Findings Report Templates (6)
- Password Attack Tools (4)
- Shell Tools + Blackarch's Webshells Collection (4)
- Walk Throughs & Pentest Processing Helpers (3)
- Encryption/Decryption Tools (2)
- Social Engineering tools (1)
- All you need as Privilege Escalation scripts and exploits
- Information Gathring Tools (21)
- Web Hacking Tools(15)
- Reverse Engineering Tools (15)
- Exploitation Tools (6)
- Pentesting & Security Assessment Findings Report Templates (6)
- Password Attack Tools (4)
- Shell Tools + Blackarch's Webshells Collection (4)
- Walk Throughs & Pentest Processing Helpers (3)
- Encryption/Decryption Tools (2)
- Social Engineering tools (1)
- All you need as Privilege Escalation scripts and exploits
- Working on Kali,Ubuntu,Arch,Fedora,Opensuse and Windows (Cygwin)
Xploit Lab : https://xploitlab.com/lockdoor-framework-penetration-testing-framework-with-cyber-security-resources/
Station X : https://www.stationx.net/threat-intelligence-17th-september/
Kelvin Security : https://blog.kelvinsecurity.com/2019/09/12/lookdoor-framework-a-penetration-testing-framework-with-cyber-security-resources/
All About hacking : https://www.allabouthack.com/2019/09/lookdoor-framework-penetration-testing.html
- Social networks :
- Twitter :
- By Me :D : https://twitter.com/S0fianeHamlaoui/status/1173079963567820801
- National Cyber Security Services : https://twitter.com/NationalCyberS1/status/1173917454151475202
- Xploit Lab : https://twitter.com/xploit_lab/status/1173990273644261376
- More : https://twitter.com/search?q=Lockdoor%20Framework
- More : https://twitter.com/search?q=Lookdoor%20Framework
- Facebook :
- By ME :D : https://www.facebook.com/S0fianeHamlaoui/posts/678704759315090
- National Cyber Security Services : https://www.facebook.com/ncybersec/posts/1273735519463836
- Xploit Lab : https://www.facebook.com/XploitLab/posts/2098443780463126
- Root Developers : https://www.facebook.com/root.deve/posts/1181412315364265
- More : https://www.facebook.com/search/top/?q=Lockdoor%20Framework
- Youtube :
- My youtube video : https://www.youtube.com/watch?v=_agvb29FQrs
- The Shadow Brokers video : https://www.youtube.com/watch?v=6njKRrKQtow
LockDoor is a Framework aimed at helping penetration testers, bug bounty hunters And cyber security engineers. This tool is designed for Debian/Ubuntu/ArchLinux based distributions to create a similar and familiar distribution for Penetration Testing. But containing the favorite and the most used tools by Pentesters. As pentesters, most of us has his personal ' /pentest/ ' directory so this Framework is helping you to build a perfect one. With all of that ! It automates the Pentesting process to help you do the job more quickly and easily.
Added value : (what makes it different from other frameworks).
- Tools ?: Lockdoor doesn't contain all pentesting tools (Added value) , let's be honest ! Who ever used all the Tools you find on all those Penetration Testing distributions ? Lockdoor contains only the favorite (Added value) and the most used toolsby Pentesters (Added value).
- what Tools ?: the tools contains Lockdoor are a collection from the best tools (Added value) on Kali,Parrot Os and BlackArch. Also some private tools (Added value) from some other hacking teams (Added value) like InurlBr, iran-cyber. Without forgeting some cool and amazing tools I found on Github made by some perfect human beigns (Added value).
- Easy customization: Easily add/remove tools. (Added value)
- Installation: You can install the tool automatically using the installer.sh , Manually or on Docker [COMING SOON]
- Resources: That's what makes Lockdoor Added value, Lockdoor Doesn't contain only tools ! Pentesing and Security Assessment Findings Reports templates (Added value) , Pentesting walkthrough examples and tempales (Added value) and more.
- Cheatsheets: Everyone can forget something on processing or a tool use, or even some trciks. Here comes the Cheatsheets (Added value) role ! there are cheatsheets about everything, every tool on the framework and any enumeration,exploitation and post-exploitation techniques.
| Kali Linux | Ubuntu | Arch Linux | Fedora | Opensuse | Windows (Cygwin) |
|---|---|---|---|---|---|
 |
 |
 |
 |
 |
 |
The recommended way to use Lockdoor is by pulling the Docker Image so you will not have to worry about dependencies issues.
A Docker image is available on Docker Hub and automatically re-built at each update: https://hub.docker.com/r/sofianehamlaoui/lockdoor. It is initially based on the official debian docker image (debian).
Docker Installation
Installing requirments
sudo apt install docker < Debian-based distributions sudo dnf install docker < RPM-based distributions sudo pacman -S docker < Arch-based distributions sudo zypper install docker < OS-based distributions sudo yum install docker < RH-based distributions
Using lockdoor's docker version
Pull lockdoor Docker Image:
sudo docker pull sofianehamlaoui/lockdoorRun fresh Docker container:
sudo docker run -it --name lockdoor-container -w /Lockdoor-Framework --net=host sofianehamlaoui/lockdoorRun Lockdoor Framework
lockdoorTo re-run a stopped container:
sudo docker start -i sofianehamlaoui/lockdoorTo open multiple shells inside the container:
sudo docker exec -it lockdoor-container bash
Automatically
1) Automatically(x2) installation : bash <(wget -qO- https://git.io/JUBlZ) 2) Automatically(x1) installation : git clone https://github.com/SofianeHamlaoui/Lockdoor-Framework.git && cd Lockdoor-Framework chmod +x ./install.sh ./install.sh
Manually
Installing requirments
python python-pip python-requests python2 python2-pip gcc ruby php git wget bc curl netcat subversion jre-openjdk make automake gcc linux-headers gzipInstalling Go
wget https://dl.google.com/go/go1.13.linux-amd64.tar.gz tar -xvf go1.13.linux-amd64.tar.gz mv go /usr/local export GOROOT=/usr/local/go export PATH=$GOPATH/bin:$GOROOT/bin:$PATH rm go1.13.linux-amd64.tar.gz
Installing Lockdoor
# Clonnig git clone https://github.com/SofianeHamlaoui/Lockdoor-Framework.git && cd Lockdoor-Framework # Create the config file # INSTALLDIR = where you want to install Lockdoor (Ex : /opt/sofiane/pentest) echo "Location:"$installdir > $HOME"/.config/lockdoor/lockdoor.conf" # Moving the resources folder mv ToolsResources/* INSTALLDIR # Installing Lockdoor from PyPi pip3 install lockdoor
- Tools:
- dirsearch : A Web path scanner
- brut3k1t : security-oriented bruteforce framework
- gobuster : DNS and VHost busting tool written in Go
- Enyx : an SNMP IPv6 Enumeration Tool
- Goohak : Launchs Google Hacking Queries Against A Target Domain
- Nasnum : The NAS Enumerator
- Sublist3r : Fast subdomains enumeration tool for penetration testers
- wafw00f : identify and fingerprint Web Application Firewall
- Photon : ncredibly fast crawler designed for OSINT.
- Raccoon : offensive security tool for reconnaissance and vulnerability scanning
- DnsRecon : DNS Enumeration Script
- Nmap : The famous security Scanner, Port Scanner, & Network Exploration Tool
- sherlock : Find usernames across social networks
- snmpwn : An SNMPv3 User Enumerator and Attack tool
- Striker : an offensive information and vulnerability scanner.
- theHarvester : E-mails, subdomains and names Harvester
- URLextractor : Information gathering & website reconnaissance
- denumerator.py : Enumerates list of subdomains
- other : other Information gathering,recon and Enumeration scripts I collected somewhere.
- Frameworks:
- ReconDog : Reconnaissance Swiss Army Knife
- RED_HAWK : All in one tool for Information Gathering, Vulnerability Scanning and Crawling
- Dracnmap : Info Gathering Framework
- Tools:
- Spaghetti : Spaghetti - Web Application Security Scanner
- CMSmap : CMS scanner
- BruteXSS : BruteXSS is a tool to find XSS vulnerabilities in web application
- J-dorker : Website List grabber from Bing
- droopescan : scanner , identify , CMSs , Drupal , Silverstripe.
- Optiva : Web Application Scanne
- V3n0M : Pentesting scanner in Python3.6 for SQLi/XSS/LFI/RFI and other Vulns
- AtScan : Advanced dork Search & Mass Exploit Scanner
- WPSeku : Wordpress Security Scanner
- Wpscan : A simple Wordpress scanner written in python
- XSStrike : Most advanced XSS scanner.
- Sqlmap : automatic SQL injection and database takeover tool
- WhatWeb : the Next generation web scanner
- joomscan : Joomla Vulnerability Scanner Project
- Frameworks:
- Dzjecter : Server checking Tool
- Radare2 : unix-like reverse engineering framework
- VirtusTotal : VirusTotal tools
- Miasm : Reverse engineering framework
- Mirror : reverses the bytes of a file
- DnSpy : .NET debugger and assembly
- AngrIo : A python framework for analyzing binaries ( Suggested by @Hamz-a )
- DLLRunner : a smart DLL execution script for malware analysis in sandbox systems.
- Fuzzy Server : a Program That Uses Pre-Made Spike Scripts to Attack VulnServer.
- yara : a tool aimed at helping malware researchers toidentify and classify malware samples
- Spike : a protocol fuzzer creation kit + audits
- other : other scripts collected somewhere
- Findsploit : Find exploits in local and online databases instantly
- Pompem : Exploit and Vulnerability Finder
- rfix : Python tool that helps RFI exploitation.
- InUrlBr : Advanced search in search engines
- Burpsuite : Burp Suite for security testing & scanning.
- linux-exploit-suggester2 : Next-Generation Linux Kernel Exploit Suggester
- other : other scripts I collected somewhere.
- WebShells : BlackArch's Webshells Collection
- ShellSum : A defense tool - detect web shells in local directories
- Weevely : Weaponized web shell
- python-pty-shells : Python PTY backdoors
- crunch : a wordlist generator
- CeWL : a Custom Word List Generator
- patator : a multi-purpose brute-forcer, with a modular design and a flexible usage
- Codetective : a tool to determine the crypto/encoding algorithm used
- findmyhash : Python script to crack hashes using online services
- scythe : an accounts enumerator
- Cheatsheet_SMBEnumeration
- configuration_management
- dns_enumeration
- file_enumeration
- http_enumeration
- information_gathering_owasp_guide
- miniserv_webmin_enumeration
- ms_sql_server_enumeration
- nfs_enumeration
- osint_recon_ng
- passive_information_gathering
- pop3_enumeration
- ports_emumeration
- rpc_enumeration
- scanning
- smb_enumeration
- smtp_enumeration
- snmb_enumeration
- vulnerability_scanning
- Demo Company - Security Assessment Findings Report.docx
- linux-template.md
- PWKv1-REPORT.doc
- pwkv1_report.doc
- template-penetration-testing-report-v03.pdf
- windows-template.md
- OSCP-OS-XXXXX-Lab-Report_Template3.2.docx
- OSCP-OS-XXXXX-Exam-Report_Template3.2.docx
- CherryTree_template.ctb
- eventory-sample-pentest-report.pdf
- auxiliary_info.md
- Cheatsheet_ApacheSSL
- Cheatsheet_AttackingMSSQL
- Cheatsheet_DomainAdminExploitation
- Cheatsheet_SQLInjection
- Cheatsheet_VulnVerify.txt
- code-execution-reverse-shell-commands
- file_upload.md
- html5_cheat_sheet
- jquery_cheat_sheet_1.3.2
- sqli
- sqli_cheatsheet
- sqli-quries
- sqli-tips
- web_app_security
- web_app_vulns_Arabic
- Xss_1
- Xss_2
- xss_actionscript
- xxe
- Fork it ( https://github.com/SofianeHamlaoui/Lockdoor-Framework/fork )
- Create your feature branch
- Commit your changes
- Push to the branch
- Create a new Pull Request



















